个人基本情况
吕明琪,教授、博导,浙江工业大学地理信息学院时空信息与智能计算研究所执行所长,浙江大学计算机科学与技术专业博士,曾任南洋理工大学计算机工程学院Research Fellow,浙江省计算机学会人机交互专委秘书长。在基础理论研究方面,长期从事时空人工智能、时空数据挖掘、数据驱动安全等领域的研究工作,主持/参与国家自然科学基金联合重点项目、国家自然科学基金面上项目、浙江省自然科学基金重点项目、浙江省“尖兵”研发攻关计划项目等省部级以上科研项目10余项。在IEEE TDSC、TIFS、TMC、TCYB、TITS、ACM CCS、KDD、UbiComp等国际顶级期刊和会议上发表学术论文100余篇(H指数23),授权国家发明专利40余项,先后获得浙江省技术发明二等奖、中国电子学会科技进步二等奖、日内瓦成果金奖、中国民营科技促进会科技进步二等奖等奖项。在行业应用研究方面,近年来聚焦低空经济、智慧城市等领域的数智化建设,承担了浙江省首个低空空域治理的“尖兵”项目,研制了“久宇”低空仿真系统、“久宇”多模态大模型、物联网时空数据运维系统等,相关成果应用在中国移动智慧家庭安全大脑、中烟工业生产运维系统、北京智网易联的“智飞”低空空域管控平台、浙江鸿程智慧城市研究院空气质量智能监测系统中。
主要研究方向
1. 低空具身智能
围绕无人机的智能导航、智慧巡检等应用,具体研究低空视觉检测模型、视觉语言导航模型、多模态融合感知算法、无人机飞控智能体等内容。

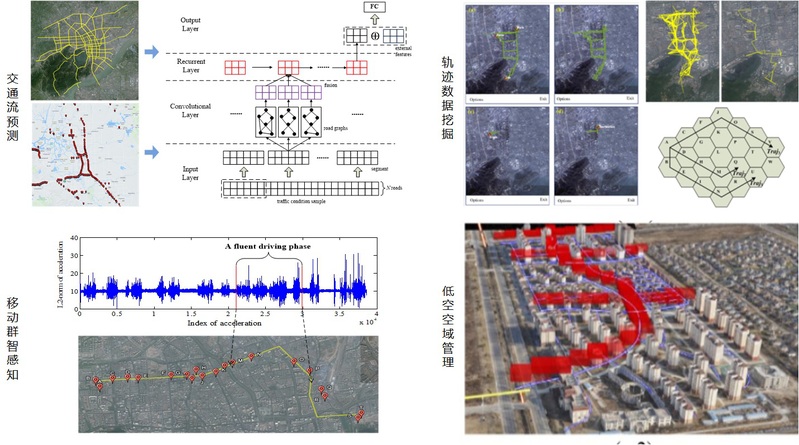
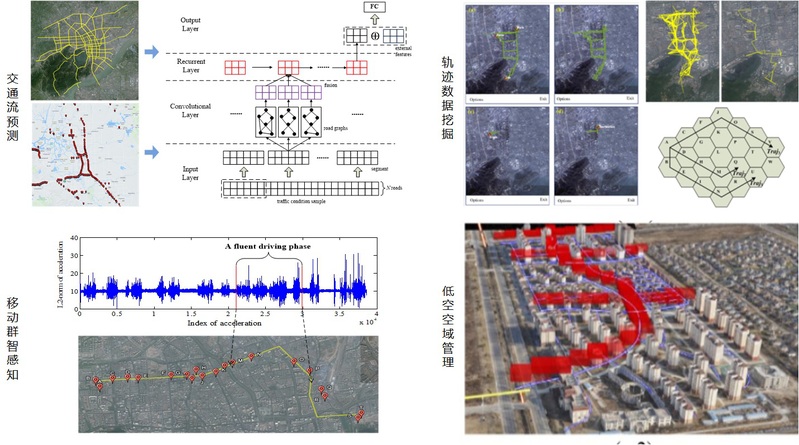
2. 时空人工智能
围绕多模态时空大模型构建的目标,具体研究面向多维时序、地理信息、视觉语言、实景三维等时空数据的大模型架构、微调、推理、智能体等的优化方法,及其在智慧城市、智慧交通、智慧环境等领域的应用。
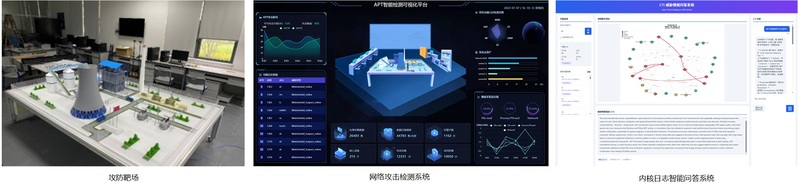
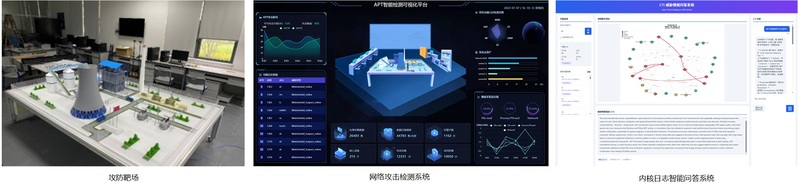
3. 智能网络安全
围绕网络攻击检测和防护的目标,具体研究融合网络流量、内核日志、软件代码等多源数据的网络攻击智能检测模型,以及基于威胁情报和大模型的网络攻击防护和运维方法。